“Malware” is a very general word for software that deliberately harms, restricts, alters, or stops your computer from working properly, and you do not give your permission for installation and use.
All infectors (worms, viruses, Trojans) are malware. Sometimes when someone downloads a “free” program from the internet, whether the program is for access to a restricted website, to play a game, or to use a peer-to-peer file sharing program, there can be compensation for the privilege of downloading the free software. This compensation can be in the form of a phone bill from a long distance internet access connection or giving your permission by marking the box that says you already read the ‘Terms of the Agreement’ or the ‘License Agreement’ before downloading. These agreements can say you are giving your permission to the company or website to track or monitor your online activities and behavior for marketing or statistical purposes; or, you are giving your permission for this company or website to use the resources of your computer.
You can recognize the possibility of adware, spyware, or malware already installed on your computer by:
the computer light blinking (meaning that your computer is processing information) at unusual or unexpected times. This is difficult to observe with broadband since there is not a visual difference between incoming and outgoing data
when the amount of pop-up advertisements is way too much or immediately begins when you connect to the internet your browser settings keep changing, including the webpage you designate as your start-up page
files are uploaded or downloaded without your prompting
Adware is software that displays advertising while it is being used. The computer user has an option to buy a license to stop the advertisements from displaying. This adware is not malware or infectious because the computer user knows that in exchange for not buying a license, they will see advertisements that the company hopes they will click on and buy the product or service. Other adware License Agreements include permissions from the user to the company for privileges stated in the agreement. The computer user should always read and understand any agreement before accepting. If you do not read and understand what you are agreeing to, you may be giving your permission, for example, to the company or third party to monitor your activities while online. This monitoring can be where you go, where you shop, or your web browsing preferences and habits. Companies find this information useful so they can generate advertisements customized specifically for your interests, likes, and dislikes. Adware is generating much discussion about balancing the rights and privacy of consumers and customers. So, be sure you read and understand all agreements before accepting them.
Spyware is tracking software that hides itself (runs in the background) and gathers information without the computer owner’s or user’s knowledge or permission for the benefit of someone else. It uses the computer owner’s internet connection to send the collected information to whomever the tracking software designates. This is the reason for the invalid default internet connection discussed in the “Home Computer Security” chapter. Spyware can compromise the safety of your passwords, logon information, financial, or personal information. Collected information can include your online habits and preferences (where you go, where you shop, for what, how much, how often, etc), each key you press on your keyboard, passwords, logon information, account and financial information,
online correspondence and conversations.
What spyware and malware have in common is the ability to collect and distribute your personal information. Malware can also send and make computer resources and information available to unknown recipients or remote users without your knowledge or permission.
Both spyware and malware are possible methods for identity theft since the computer owner or user does not know about or does not provide their permission for the installation
and use of the hidden program or file.
There are legitimate uses for spyware (monitoring software) by law enforcement, parents, and employers. If you have a court order to monitor the activities of someone; or, are legally responsible for the actions and safety of someone such as a child or employee; then, you usually have the option to monitor the online activities of that person if you own the computer or computer system where the monitoring software is installed.
Use anti-virus and spyware detection software. Be aware of how and when your computer reacts differently than its’ usual behavior. If you have any suspicions of criminal activity directed specifically towards your home computer, contact the Internet Crime Complaint Center or your local cybercrime task force.”
Spyware Related Websites
FTC Blog
Play the “Beware of Spyware” Game by the FTC
Spyware Articles
A Primer in Malware: Viruses, Spyware and Bots, Oh My!
Electronic Gifts Could Track His Moves
Researchers Find More Versions of Digitally Signed Mac OS X Spyware
Boffin’s Top Choice for Anti-Spyware This Year
New Mac Spyware Found on Angolan Activists’ Computer
Media companies want Congress to leagalize spyware, malware and other insane acts
Spyware from West used to target activists
Mozilla warns European spyware maker to stop spoofing us
Spyware used by governments poses as Firefox and Mozilla is angry
Judge denies FBI request to hijack suspect’s personal computer using spyware
‘Redpill’ spyware used for seizing information from Indian internet users
Court partially dismisses Google mobile app spyware case
How to spring-clean and revive your personal computer
Juniper Networks 740-061405 JNP-QSFP-100G-SR4 OM3 QSFP28 100GE 850nm100m 1PCS
$150.00
Factory new Sealed SRX-GP-16GE-PoE Juniper Networks expansion module
$79.00
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
Juniper Networks EX3300 EX3300-48P 48-Port Gigabit PoE+ Switch
$40.10
Juniper Networks EX4300-48T 48 Port Gigabit 4 QSFP 40G 2xPSU AFO Network Switch
$89.00
JUNIPER EX3400-48P 48x 1GB PoE+ RJ-45 4x 10GB SFP+ 2x 40GB QSFP+, DUAL AC POWER
$210.00
Juniper QFX5100-48S-3AFO Switch 48 x 10Gb SFP+, 6x QSFP 40GE, Dual AC Power
$499.00
Juniper Networks EX2300 -24P 24 Port Gigabit PoE Network Switch
$149.00
Juniper PD-4OC192-SON-XFP 710-013264 Four line-rate OC-192c/ STM-64 IPUIA01MTA
$675.00
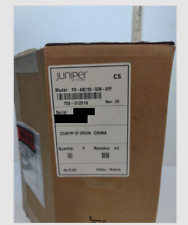
New Factory Sealed Juniper EX2300-48P Networks 48-Port Managed Ethernet Sealed
$499.00